In the field of computer science.. Cryptography refers to the security of data and communications techniques derived from the mathematical world as well as a plethora of rules based computations also known as calculations.. To transform data into ways that are difficult to decipher.
The calculations that are deterministic can be used in cryptographic key generation.. Advanced marking.. authentication to ensure the privacy of information.. Web browsing and private exchanges.. Examples include.. the exchange of credit cards and emails.
Cryptography techniques & procedures
Cryptography is tightly linked with the field of cryptology and the field of cryptanalysis. It includes strategies such as microdots.. condensing words using photographs and alternative methods to protect data from the storage space or in travel. Today in the PC driven society.. Cryptography is often associated with the process of making plaintext (customary text.. at times is referred to as plaintext ) to encrypted text (a procedure that was later reverted in the form of encryption ).. Naturally (known as scrambling). Individuals who are involved in this area are referred to as cryptographers.
The current cryptography concerns concern the associated four objectives:
* Confidentiality. The information cannot be understood by anyone who has access to it.
* Respectability. Data cannot be altered when stored or transferred between the shipper and anticipated receiver without a distinction being made between the changes.
* No repudiation. The creator/editor of the data cannot deny in the future their motives with regard to the production or transfer of information.
* Authentication. The recipient and shipper can verify each others identity and also the start/conclusion of the information.

Conventions and methods that comply with all or some of these standards are referred to as cryptosystems. They are often thought to mean computers and mathematical strategies.
Additionally they regulate of human behaviour…. such as.. selecting difficult to understand passwords.. closing off unused frameworks and not speaking about unreachable systems and sensitive systems.
Cryptography is the method of decoding and encoding data.
Cryptographic Algorithms
They employ various strategies called cryptographic calculations.. or numbers.. for encoding and decode information to ensure secure the exchange of information between computers frameworks.. Applications and gadgets.
A cipher set is comprised of an encryption calculation.. Another calculation to verify messages as well as one additional calculation to exchange keys. The process.. integrated into the conventions and written into software that results in a sudden increase in demands for operating frameworks (OSes) and computing frameworks.. This includes:
* Private and public key generation to decrypt and encrypt information.
* Electronic marking and verification of message verification.
* Exchange of keys.
Different types of cryptography
Asymmetric or single key encryption algorithms create a fixed number of blocks also known as block ciphers with secret keys which the shipper or maker uses to encode the information (encryption) and then the receiver is able to decipher the information. A good example of symmetric key encryption is the High level Encryption Standard ( AES ).
AES is a standard that was established in the month of November 2001 by the Public Foundation of Norms and Innovation (NIST) as Government Data Handling Standard (FIPS 197 ) to safeguard sensitive information. This standard was approved from the U. S. Government and is generally used for confidential purposes.
The month of June was 2003.. AES was supported by the U. S. government agency for the classification of details. AES is an open standard specialization that is used in programming and other equipment around the world. AES is a substitute for the Information Encryption Standard ( DES ) as well as DES 3. AES uses longer length keys 128 bits.. It has 192 bits.. and 256 bits in order to protect against animal power and other attacks.
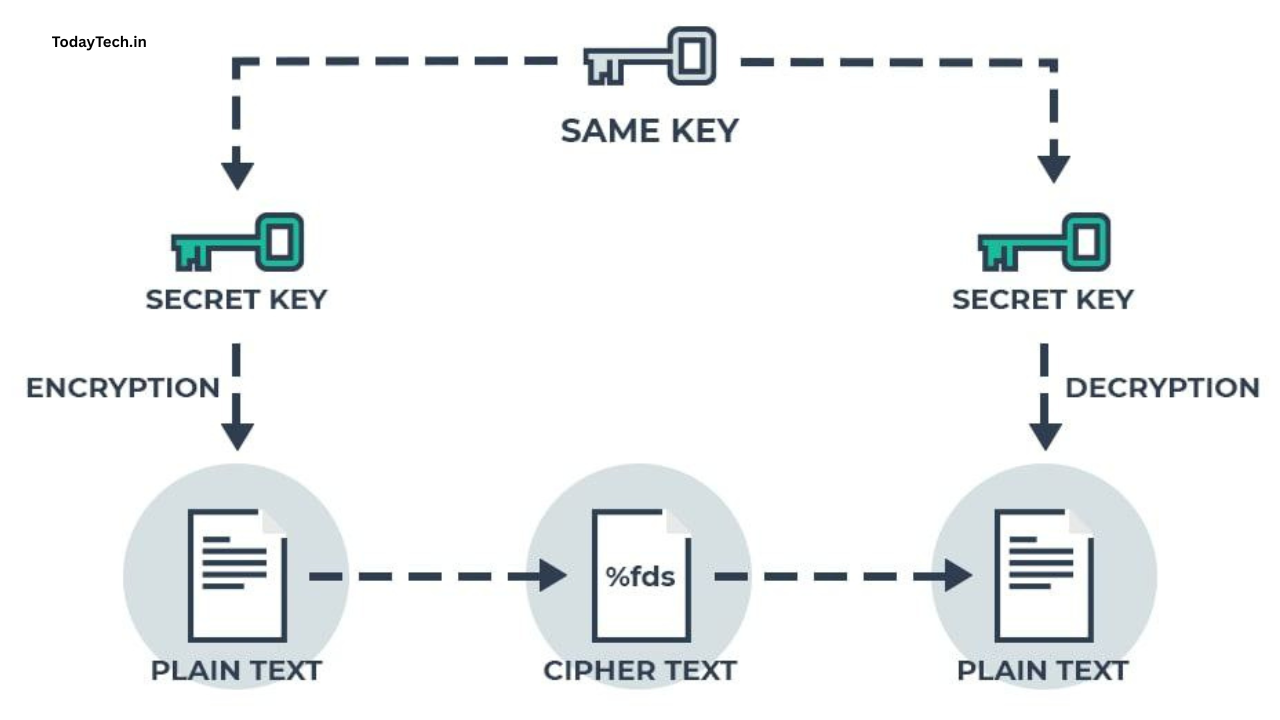
Symmetric cryptography employs one key whereas lopsided cryptography employs a keys to encode and unwrap information.
Unbalanced or public key encryption algorithms use a two keys.. Public key is associated with the creator/source used to encode messages. Private key is one that only the creator has access to (except in the event that its exposed or if they decide to share the key) to decode the data.
Public key cryptography instances can be accompanied by the following:
* RSA (Rivest Shamir Adleman).. It is used frequently on the web.
* Elliptic Bend Computerized Mark Calculation (ECDSA) is used by Bitcoin.
* Computerized Mark Calculation (DSA) accepted as a an industry standard for computerized markings by NIST in FIPS 186 4.
* Diffie Hellman key exchange.
In order to ensure the integrity of information when using the field of cryptography.. ish functions.. that provide a definite output from input values.. They are used for planning information according to a fixed dimensions. Different types of cryptographic hash capability are SHA 1 (Secure Hash Calculation 1 ).. SHA 2 and SHA 3.
Cryptography is a concern
Criminals are able to bypass the cryptography.. attack computers susceptible to information encryption and re encrypting and exploiting weaknesses in execution…. such as.. The use of standard keys. Cryptography hinders attackers to gain access to messages and the information protected with encryption algorithms.
Concerns regarding the power to handle quantum processing which could be a threat to current standard for encryption in cryptography led NIST to announce a solicitations for submissions from scientists and the mathematical community in the year 2016 to develop an open key cryptography standard. NIST has announced it will be able to provide three quantum secure cryptographic computations to be used in 2024.

In no way is it like existing computer platforms.. quantum computing uses quantum bits ( qubits ) which are able to show both the 0 and 1 seconds and consequently make two estimates for the double. Quantum computers of massive scale cannot be built over the next ten years.. the present infrastructure needs to be normalized for widely known as well as perceived calculations to provide an effective method.. According to NIST.
The history of cryptography
The term “cryptography” is gotten from the Greek”kryptos.. The importance of the word is tucked away.
“Tomb” the prefix “tomb ” signifies “stowed away” or “vault..” and the word ” graphy” means “composing.”
The genesis of cryptography can be generally dated about the year 2000 B.C… with the Egyptian use of hieroglyphics. They were made up of intricate pictograms.. The significance of which was understood by a select few.
The first recorded use of ciphers with cutting edges was made by Julius Caesar ( 100 B. C. up to 44 B. C. ).. He was distrustful of his couriers in conversations with the top officials and representatives. Because of this.. the man created an outline.
every character in the messages was substituted with a the character 3 positions prior to it. Roman characters in the order in.
In recent years.. the field of cryptography has evolved into a milestone for a portion of the top computer scientists and mathematicians. Its ability to securely store and transmit sensitive data has been a crucial to success both in business and war.
Legislative bodies do not wish particular elements throughout their countries to be able for receiving and sending away information which could pose a danger to national security.. The cryptography field has been limited in a number of nations.. From the limitations on the use and output of software to the open dissemination of ideas in numerical form which could be utilized to create cryptosystems.
The web has enabled the spreading of highly efficient programs.. regardless and even more crucially.. the secret strategies that are used in cryptography.. in the hope that the majority of the most advanced cryptosystems and ideas are publicly available.

